Application To Malicious Code Fingerprinting: Advances In Information Security 78

In the ever-evolving landscape of information security, malicious code poses a significant threat to computer systems and networks. Malicious code, often referred to as malware, encompasses a wide range of malicious software programs designed to disrupt, damage, or steal sensitive information. To combat these threats, security researchers and practitioners employ various techniques, including malicious code fingerprinting, to identify and mitigate malware attacks.
Malicious code fingerprinting is a technique used to identify and categorize malicious software based on its unique characteristics. It involves extracting distinguishing features from malware samples and using these features to create a fingerprint that can be used for identification and tracking. Malicious code fingerprinting plays a crucial role in safeguarding computer systems and networks from cyber threats by enabling security analysts to:
5 out of 5
| Language | : | English |
| File size | : | 21959 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 476 pages |
- Identify and classify malware
- Detect and prevent malware infections
- Track the spread of malware
- Attribute malware attacks to specific sources
- Improve threat intelligence and incident response
Benefits of Malicious Code Fingerprinting
Malicious code fingerprinting offers several key benefits for information security:
- Improved malware detection: Fingerprinting enables security analysts to detect and identify malware even when it evades traditional signature-based detection methods.
- Enhanced threat intelligence: By collecting and analyzing malware fingerprints, security analysts can gain valuable insights into malware trends, attack patterns, and threat actors.
- Faster incident response: Fingerprinting allows security teams to quickly identify the type of malware involved in an attack, enabling them to implement appropriate mitigation strategies.
- Attribution and tracking: Fingerprinting helps attribute malware attacks to specific sources, aiding in investigations and legal proceedings.
- Improved security research: Fingerprinting provides a valuable tool for security researchers to study malware behavior, identify new threats, and develop more effective countermeasures.
Challenges of Malicious Code Fingerprinting
Despite its benefits, malicious code fingerprinting also faces several challenges:
- Malware evolution: Malware authors constantly update and modify their code to evade detection, making it challenging to maintain accurate fingerprints.
- Large and diverse malware landscape: The sheer volume and diversity of malware make it difficult to develop comprehensive fingerprinting mechanisms.
- Resource-intensive: Fingerprinting can be computationally expensive, especially for large-scale malware analysis.
- Privacy concerns: Fingerprinting techniques may collect sensitive information from malware samples, raising privacy concerns.
Advances in Malicious Code Fingerprinting
Researchers and practitioners are actively working to address the challenges of malicious code fingerprinting and develop more effective fingerprinting techniques. Some of the recent advances in this field include:
- Machine learning and artificial intelligence: Machine learning and artificial intelligence algorithms are increasingly used to improve the accuracy and efficiency of malicious code fingerprinting.
- Behavioral fingerprinting: Behavioral fingerprinting techniques focus on identifying malware based on its behavior and interactions with the system, rather than its static code characteristics.
- Collaborative fingerprinting: Collaborative fingerprinting initiatives, such as the Malware Information Sharing Platform (MISP),enable security researchers and organizations to share malware fingerprints and threat intelligence.
- Cloud-based fingerprinting services: Cloud-based fingerprinting services provide scalable and cost-effective solutions for large-scale malware analysis and fingerprinting.
Significance of Malicious Code Fingerprinting for Information Security
Malicious code fingerprinting is a vital component of a comprehensive information security strategy. By enabling security analysts to identify, track, and mitigate malware threats, fingerprinting plays a crucial role in protecting computer systems and networks from cyber attacks. As the threat landscape continues to evolve, malicious code fingerprinting will become increasingly important for safeguarding information security and ensuring the integrity and confidentiality of sensitive data.
Implementing Effective Malicious Code Fingerprinting
To implement effective malicious code fingerprinting, organizations should consider the following best practices:
- Use a multi-layered approach: Combine fingerprinting techniques with other security measures, such as signature-based detection, intrusion detection systems, and sandboxing, to provide comprehensive protection.
- Keep fingerprints up to date: Regularly update malware fingerprints to stay ahead of evolving threats.
- Share threat intelligence: Participate in collaborative fingerprinting initiatives to share threat intelligence and improve the overall effectiveness of fingerprinting.
- Consider privacy implications: Implement fingerprinting mechanisms that respect user privacy and comply with relevant data protection regulations.
- Invest in research and development: Support research and development efforts to advance the field of malicious code fingerprinting and develop more effective techniques.
Malicious code fingerprinting is a powerful technique that
5 out of 5
| Language | : | English |
| File size | : | 21959 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 476 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Chapter
Chapter Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Shelf
Shelf Glossary
Glossary Preface
Preface Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Bestseller
Bestseller Narrative
Narrative Biography
Biography Autobiography
Autobiography Reference
Reference Encyclopedia
Encyclopedia Resolution
Resolution Card Catalog
Card Catalog Archives
Archives Study
Study Research
Research Scholarly
Scholarly Academic
Academic Rare Books
Rare Books Interlibrary
Interlibrary Literacy
Literacy Study Group
Study Group Dissertation
Dissertation Storytelling
Storytelling Awards
Awards Reading List
Reading List Theory
Theory Richard Paul Evans
Richard Paul Evans David Fulford
David Fulford Jason Blair
Jason Blair James Eells
James Eells Gregory Brown
Gregory Brown Sarra Jenkins
Sarra Jenkins Patrick Webster
Patrick Webster Bertrand Puard
Bertrand Puard Julia Kiernan
Julia Kiernan Matthew Biberman
Matthew Biberman Bob Ossler
Bob Ossler Derek Coburn
Derek Coburn Sassa Daniels
Sassa Daniels Alasdair Gray
Alasdair Gray John Merchant
John Merchant Anne Marie Meyer
Anne Marie Meyer Laura Mcgee Kvasnosky
Laura Mcgee Kvasnosky Clifford A Hull
Clifford A Hull L M Reid
L M Reid Allan R Wallace
Allan R Wallace
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Graham BlairUnveiling the Enigma of Human Genetics: A Comprehensive Guide to Genetics and...
Graham BlairUnveiling the Enigma of Human Genetics: A Comprehensive Guide to Genetics and... Aldous HuxleyFollow ·5.7k
Aldous HuxleyFollow ·5.7k Al FosterFollow ·6.8k
Al FosterFollow ·6.8k Natsume SōsekiFollow ·8.1k
Natsume SōsekiFollow ·8.1k Jaime MitchellFollow ·9.9k
Jaime MitchellFollow ·9.9k Carlos FuentesFollow ·5.8k
Carlos FuentesFollow ·5.8k Clinton ReedFollow ·11.7k
Clinton ReedFollow ·11.7k Camden MitchellFollow ·4.3k
Camden MitchellFollow ·4.3k Mario Vargas LlosaFollow ·13.3k
Mario Vargas LlosaFollow ·13.3k
 Charlie Scott
Charlie ScottAn Extensive Guide to Road Races in the Southern United...
Welcome to the...
 Seth Hayes
Seth HayesHow to Create Your Cosmetic Brand in 7 Steps: A...
The cosmetic industry is booming, with an...
 Emilio Cox
Emilio CoxLean for Dummies: A Comprehensive Guide to the Lean...
Lean is a management...
 Dashawn Hayes
Dashawn HayesThe Family She Never Met: An Enthralling Novel of...
Prologue: A Serendipitous...
 Italo Calvino
Italo CalvinoThe Alluring Soundscape of Rickie Lee Jones: A Journey...
: The Enigmatic Soul of...
 Fyodor Dostoevsky
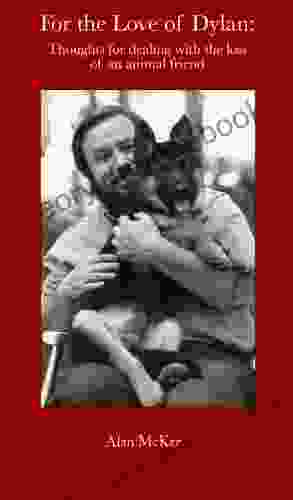
Fyodor DostoevskyFor The Love Of Dylan: An Exploration of Bob Dylan's...
Bob Dylan, the...
5 out of 5
| Language | : | English |
| File size | : | 21959 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 476 pages |