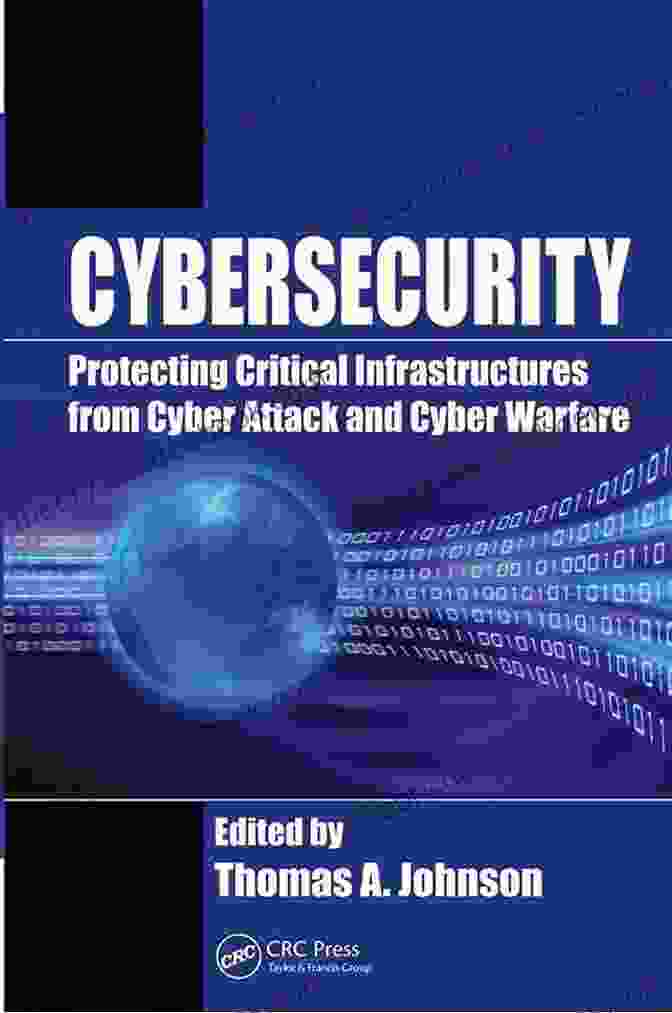
Protecting Critical Infrastructures from Cyber Attack and Cyber Warfare Zones

Critical infrastructures are essential to the functioning of modern society. They provide us with water, electricity, transportation, and communication. As we become increasingly reliant on technology, our critical infrastructures are becoming increasingly vulnerable to cyber attacks.
Cyber attacks can come in many forms, from simple denial-of-service attacks to sophisticated malware attacks that can take control of entire systems. They can be launched from anywhere in the world, and they can be difficult to detect and stop.
4.6 out of 5
| Language | : | English |
| File size | : | 13512 KB |
| Print length | : | 363 pages |
| Screen Reader | : | Supported |
The consequences of a successful cyber attack on a critical infrastructure can be devastating. For example, a cyber attack could shut down the power grid, causing widespread blackouts. It could also disrupt water supplies, transportation systems, or communication networks.
The threat of cyber attacks is real and growing. In recent years, there have been a number of high-profile cyber attacks on critical infrastructures around the world. For example, in 2015, hackers attacked the Ukrainian power grid, causing widespread blackouts. In 2016, hackers attacked the Bangladesh central bank, stealing $81 million.
These attacks are a wake-up call for governments and businesses around the world. We need to take steps to protect our critical infrastructures from cyber attacks.
How to Protect Critical Infrastructures from Cyber Attacks
There are a number of things that can be done to protect critical infrastructures from cyber attacks. These include:
- Implementing strong cybersecurity measures. This includes using firewalls, intrusion detection systems, and anti-malware software.
- Educating employees about cybersecurity risks. Employees need to be aware of the risks of cyber attacks and how to protect themselves from them.
- Developing incident response plans. In the event of a cyber attack, it is important to have a plan in place to respond quickly and effectively.
- Working with government and law enforcement. Governments and law enforcement agencies can play a role in protecting critical infrastructures from cyber attacks.
Cyber Warfare Zones
Cyber warfare zones are areas where there is a high risk of cyber attacks. These areas may include:
- Countries with a history of cyber attacks.
- Countries with a large number of critical infrastructures.
- Countries with a weak cybersecurity posture.
Businesses and governments need to be aware of the risks of cyber attacks in cyber warfare zones. They should take steps to protect their critical infrastructures from these attacks.
Cyber attacks are a serious threat to our critical infrastructures. We need to take steps to protect these infrastructures from these attacks. By implementing strong cybersecurity measures, educating employees about cybersecurity risks, developing incident response plans, and working with government and law enforcement, we can help to keep our critical infrastructures safe from cyber attacks.
Additional Resources
* Cybersecurity and Infrastructure Security Agency (CISA) * Federal Bureau of Investigation (FBI) Cyber Division * Internet Crime Complaint Center (IC3)
4.6 out of 5
| Language | : | English |
| File size | : | 13512 KB |
| Print length | : | 363 pages |
| Screen Reader | : | Supported |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Story
Story Genre
Genre Paperback
Paperback Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Synopsis
Synopsis Manuscript
Manuscript Scroll
Scroll Bestseller
Bestseller Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Card Catalog
Card Catalog Borrowing
Borrowing Stacks
Stacks Archives
Archives Periodicals
Periodicals Research
Research Scholarly
Scholarly Lending
Lending Reserve
Reserve Academic
Academic Journals
Journals Reading Room
Reading Room Literacy
Literacy Study Group
Study Group Thesis
Thesis Dissertation
Dissertation Awards
Awards Reading List
Reading List Book Club
Book Club Luca Mavelli
Luca Mavelli John Stovall
John Stovall Charles Dagher
Charles Dagher Jaideep Hardikar
Jaideep Hardikar Cindy Maddox
Cindy Maddox Lance Mckinzie
Lance Mckinzie Michael Nest
Michael Nest Andres Miedoso
Andres Miedoso Bob Shea
Bob Shea Karen Musgrave
Karen Musgrave Elisabeth Katz
Elisabeth Katz Danny White
Danny White Lori Wilde
Lori Wilde Debbie Bauer
Debbie Bauer Andrea Barrett
Andrea Barrett Pete Hautman
Pete Hautman Anne Peckham
Anne Peckham Josie Ford
Josie Ford Royden Lepp
Royden Lepp Jeff Fisher
Jeff Fisher
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Reginald CoxFollow ·18.8k
Reginald CoxFollow ·18.8k Frank MitchellFollow ·7.7k
Frank MitchellFollow ·7.7k Nick TurnerFollow ·11.8k
Nick TurnerFollow ·11.8k Ken SimmonsFollow ·3.2k
Ken SimmonsFollow ·3.2k Craig BlairFollow ·5.4k
Craig BlairFollow ·5.4k Junichiro TanizakiFollow ·19.3k
Junichiro TanizakiFollow ·19.3k Gary CoxFollow ·16.3k
Gary CoxFollow ·16.3k Bryan GrayFollow ·12.6k
Bryan GrayFollow ·12.6k
 Charlie Scott
Charlie ScottAn Extensive Guide to Road Races in the Southern United...
Welcome to the...
 Seth Hayes
Seth HayesHow to Create Your Cosmetic Brand in 7 Steps: A...
The cosmetic industry is booming, with an...
 Emilio Cox
Emilio CoxLean for Dummies: A Comprehensive Guide to the Lean...
Lean is a management...
 Dashawn Hayes
Dashawn HayesThe Family She Never Met: An Enthralling Novel of...
Prologue: A Serendipitous...
 Italo Calvino
Italo CalvinoThe Alluring Soundscape of Rickie Lee Jones: A Journey...
: The Enigmatic Soul of...
 Fyodor Dostoevsky
Fyodor DostoevskyFor The Love Of Dylan: An Exploration of Bob Dylan's...
Bob Dylan, the...
4.6 out of 5
| Language | : | English |
| File size | : | 13512 KB |
| Print length | : | 363 pages |
| Screen Reader | : | Supported |